If you should "come across" an image of sexy Russian supermodel Irina Shayk, beware. Bad Guys are using R-rated photos of Ms. Shayk to spread Mac malware.
Didn't your mom tell you not to download pictures of naked ladies? But you didn't listen, did you?
It turns out that a group of hackers is taking advantage of that common mistake and snaring Mac users in a malware trap baited with pictures of a topless Sports Illustrated swimsuit model.
The lady in question is Russian model Irina Shayk; the malware is OSX/Imuler-B, a Trojan horse, according to Graham Cluley, who blogs for Sophos , a security vendor. If you yield to temptation and click the tainted photo of Ms. Shayk, the malware launches an application that opens a backdoor to your computer and uploads private information to a remote Web server, he says. It can also take screenshots and send them to the server, another security firm found.
Although malware that targets Macs isn't as common as Windows malware, Mac users who think they are immune are simply wrong. The Mac OS is not immune to attack, and one of the main reasons it isn't targeted more often is that hackers prefer to attack the platform with the most users. And that's Windows.
The increasing popularity of Macs and mobile devices running Apple's iOS has led to an increase in iOS and Mac attacks. And like attacks directed at Windows, attacks against Macs often use social engineering to snare victims. By social engineering, I mean a ploy that tricks a user into thinking he or she is clicking on a file from a business or person they know, or a trick that plays upon greed (You've won $1 million!) or curiosity, or in this case, lust--or at least a desire to see unclothed females.
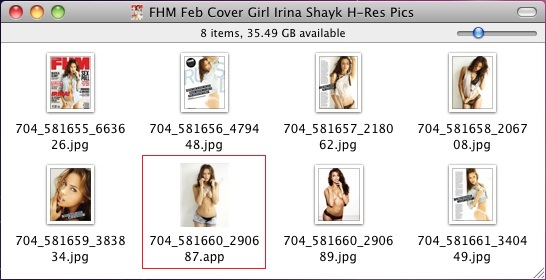
It appears that the malware was first discovered by researchers from Intego, a company that specializes in Mac security. "Two samples were found, both in zip archives: 'Pictures and the Article of Renzin Dorjee.zip' and 'FHM Feb Cover Girl Irina Shayk H-Res Pics.zip.' In both cases, an application was included among the various files, with an icon making it look like an image," Intego reported in its security blog.
The hackers are taking advantage of a default setting in the Mac OS X Finder, whereby file extensions are not displayed. "Users double-click on the application to launch the malware, which quickly deletes itself, replacing the original application with a real JPEG image corresponding to the one that was an application, and displays this image in the user’s default image viewer. There is no visible trace of the application after this point," according to Intego's website.
In addition to the usual advice not to click on stuff from people you don't know, Intego had a very specific tip for Mac users: Go into the Finder's advanced settings and check the box that allows you to view filename extensions.
If you're curious, you can find out all about Irina Shayk with a simple Google search, but do be careful if you come across a site that promises nude photos of the model.

I won't defend Apple on this issue.
ReplyDeleteWhen Apple transitioned from the original Mac OS to to OS X years ago, they blew it when they decided to hide file extensions by default. Extensions had been unnecessary and rarely used on the original Mac OS. They were not prohibited or hidden, -- just ignored. Apple instead had employed a system of file type and creator code metadata that was completely independent from the file name, but was unfortunately not supported by other file systems.
OS X took the pragmatic approach of deprecating type and creator codes for Unix legacy reasons, and in order to enhance cross-platform interoperability. It certainly worked, but old timers like myself were horrified. In a misguided attempt to placate us, they hid the extensions by default. Bad move. My problem with extensions had less to do with their ugliness and ease of corruption, and rather that they weren't as powerful as separate type and creator codes.
True, with file extensions hidden, novices aren't tempted to do silly stuff like trying to change a jpg to a gif simply by editing its file extension, but now we have these exploits that take advantage of the fact that the full filename isn't visible by default.
Its fine to hide complexity in some cases, but this isn't one of them. I always advise Mac users to show file extensions (ugly and primitive as they are).
Hello mate nice ppost
ReplyDelete